本文为看雪论坛优秀文章
看雪论坛作者ID:kxliping
研究攻击案例的主要目的在于“知攻”,也就是搞清楚攻击者是如何攻破车辆、实现控车的。关于对特斯拉的攻击研究,腾讯的科恩实验室贡献了几个成功的案例,按道理讲应该先解读科恩系列。但是,作为一名车联网安全工程师,我对攻击者的完整尝试路径更感兴趣,因为完整的尝试路径包含丰富的对抗信息,包括车辆的哪些防护手段有力地击退了攻击者,哪些防护手段缺失或者存在缺陷,最有效的防护手段是什么等等,而科恩的报告对这部分信息的描述甚少。因此,本文选取Pentest Partners的《Reverse Engineering Tesla Hardware》作为解读系列的开篇,一方面尝试解释清楚Pentest Partners的攻击过程,另一方面,也是我的主要目的,试图发掘真实攻击场景下,车联网安全防护技术的实际防护效果,并探索防护失效的深层次原因。Pentest Partners的完整报告由两篇文章组成:《Reverse Engineering Tesla Hardware》、《Reverse Engineering the Tesla Firmware Update Process》,前者描述了从拆件到还原硬件架构的过程,后者描述了通过逆向FOTA发现和利用漏洞的过程。本文主要解读第一篇,该篇对车载芯片的拆解和逆向探索的过程记录详细,堪称教科书式的板级逆向。书归正传,文归正叙,下面开始解读。
2.1 不设防的物理接触之一:即拆即得的PCB
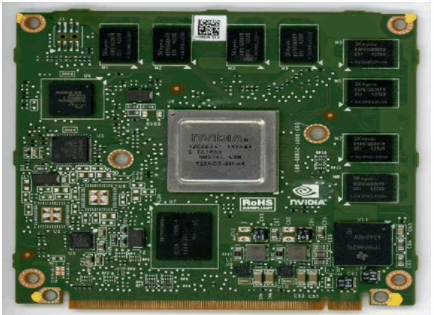
“We took the CID out of the Tesla to power it up and examine it.” (实物图片均来自Pentest Partners博客,后文不再说明)
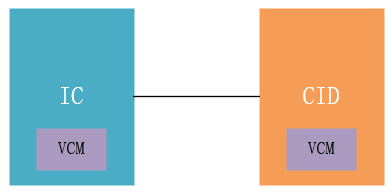
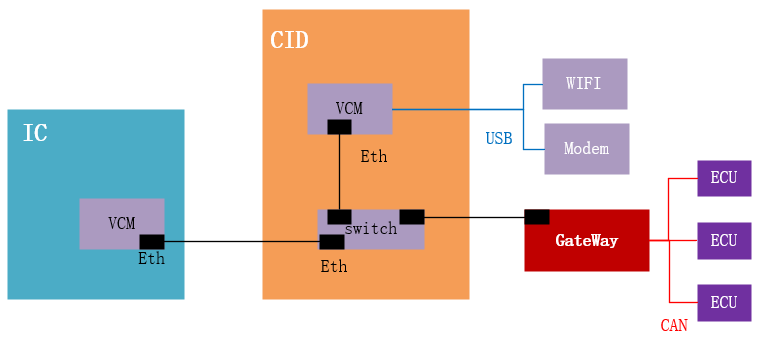
拆解后可以看到两块主要的芯片:IC和CID。IC即Instrument Cluster,仪表盘;CID即Central Information Display,中央信息显示器,即特斯拉娱乐屏背后的计算芯片。关于IC和CID的确认过程没有太多的描述,可能是根据公开信息获取,也可能是根据芯片上的标记获取。2.2 “自报家门”第一弹:算力担当VCM的信息确认
根据芯片上的文字和标致,研究员确认了VCM在IC和CID两处的存在:“An NVidia VCM (Visual Compute Module) sits at the core of the CID. This is an ARM based single-board computer module that runs Linux – the operating system that drives most of the visible actions of the Tesla.
Nvidia VCM modules are used in both the CID and IC.”“An Nvidia Tegra System-on-Chip (SoC) is used in the VCM. This has a multi-core ARM processor, GPU and various other audio and video accelerators.”VCM的SOC确认为Nvidia Tegra,多核ARM处理器,包含GPU和audio、vidio加速器。这部分信息来自Nvidia Tegra的文件描述,推测来自网络。芯片上的标致和文字明确地公开了芯片的身份信息,这种信息至少有助于理解IC和CID的电器架构。我们可以看出VCM为IC和CID提供了主要的运算能力,CID上的VCM主要为娱乐屏的图像、视频和音频提供算力支撑。2.3 第一次挫败“近亲”研究:没有关键共性的“远房亲戚”
确认VCM的SOC之后,研究员对Tesla VCM和Audi、BMW及Lamborghini在使用Nvidia VCM上的共性做了简单阐述。“Audi, BMW and Lamborghini have all been associated with Nvidia VCMs. For example, we uncovered a similar module in an Audi Virtual Cockpit.”接着,研究员对VCM的算力和其他IVI的算力做了一个简单的对比:
“It is significantly more powerful than SoCs used in other IVIs that we have examined, which is probably due to the large CID display. ”虽然在VCM的共性研究和算力对比上没有发现安全的突破口,但千万不要小看这种分析,在逆向分析的过程中,通过对相同或相近对象的比较研究,极有可能发现关键信息。在板级的对比研究中没有获取关键信息,研究员进一步尝试寻找芯片级的“近亲”。2.4 第二次挫败“近亲”研究:NDA协议的功劳
研究员进一步尝试通过开发用的相近SOC,以及使用相同系列芯片的SOC寻找关于芯片管脚和布线的信息,但是发现都需要和供应商签署NDA才能获取。“ You can obtain technical reference manuals for the Tegra 2, 3 and 4 SoC lines, but they don’t contain ball-maps or pin-outs, so are of limited use for reverse engineering.To gain access to documentation and forums, a valid developer account was created for Nvidia.com, but we could only find one reference for VCMs or the Jetson Pro development kit. We wrote a forum post asking about documentation but got no response. We envisage that an NDA would have to be signed to gain access to anything significant but it is unlikely that we would be able to share any of the information with third parties.”2.5 “自报家门”第二弹:VCM子模块信息确认
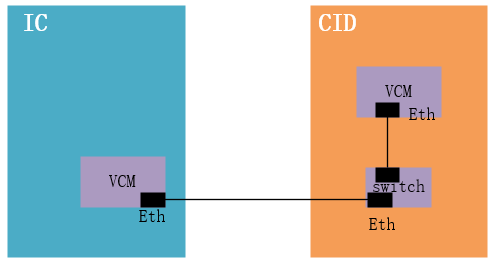
接着研究员对IC和CID上VCM挂载的子模块信息做了一遍梳理,包括NOR Flash存储器、eMMC存储器、以太网控制器、USB收发器、SDRAM存储器、电源管理模块等等。1)IC上使用的Tegra 2,比CID上Tegra 3低一个版本;这些差异表明,CID VCM承载的业务负载要高于IC VCM,即CID VCM为整个车机的主要算力单元。另外,两个VCM都挂载了以太网收发器。2.6 成本战的第一次胜利:阻止对VCM的直接分析
梳理完VCM上的子模块之后,研究员的下一步计划是对VCM做侵入性分析。虽然研究员已经通过示波器确认了电源引脚,但是3000到10000英镑的维修成本使研究员放弃了对VCM的直接分析。“We believe that the pin-outs of the two VCMs were the same – voltage supply and ground appeared to be on the same pins, which was confirmed with an oscilloscope. We did not want to direct test the VCMs from the Tesla due to risk of damaging or bricking the CID or IC. This could make the car unusable, and cost somewhere between £3,000 and £10,000 to have repaired by Tesla.”2.7 被“近亲”研究突突了一小步:VCM固件被提取,零部件生命周期的锅
在前面几次寻找相近型号芯片的尝试失败后,研究员不知从哪淘来一块二手的VCM,这块二手VCM除了RAM容量和IC VCM不一样,其他子模块基本完全一致。“we obtained a third VCM from a second-hand IC. This was the same as the VCM in the IC from the test, except it had 50% less RAM. The IC itself was a different model. We conducted invasive testing”研究员从这块二手TCM的Nor Flash中提取了第一、第二阶段的bootloader,kernel以及boot相关的数据,其他文件系统相关的数据则存在于NAND Flash中,文件系统的其余部分位于NAND闪存中。大多数文件存储在压缩的只读文件系统 (squashfs) 中,小部分存储在读/写文件系统 (ext4) 中。
2.8 “自报家门”第二弹:SWITCH信息确认
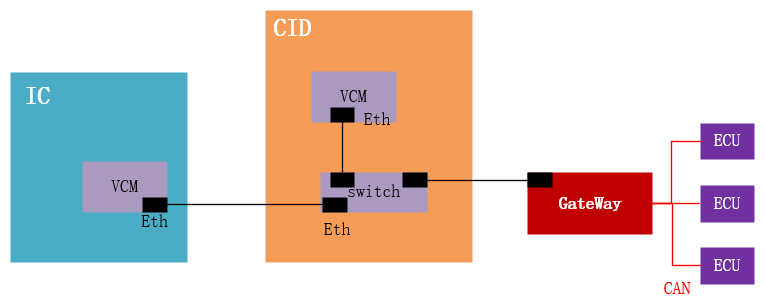
通过Switch芯片上的文字和标致信息,研究员确认了Switch为Marvell 88E6061,支持VLAN:“A built-in Ethernet switch connects the VCM to the rest of the vehicle via a Marvell 88E6061. This five-port 10/100 switch supports VLANs. It is configured using SMI, a serial interface. The Ethernet switch is configured when the CID starts.”2.9 通信协议的第一次破防:可以被嗅探和篡改的SMI
SMI通信缺乏有效的安全措施,研究员可以通过逻辑分析仪嗅探SMI命令,并篡改SMI指令。虽然通过VLAN划分了广播域,但由于SMI命令缺乏完整性保护,导致可以通过篡改指令修改VLAN配置。“A logic analyser could sniff the SMI commands. We could not ascertain whether they were sent by the VCM or the gateway processor. Traffic is segregated from the various components using several VLANs.There is no security functionality associated with the SMI, for example integrity protection – it trusts all signals, meaning that communications can be tampered with or modified. VLAN configuration could be modified in this way, potentially creating new routes into the system. ”2.10 “自报家门”第三弹:网关信息确认
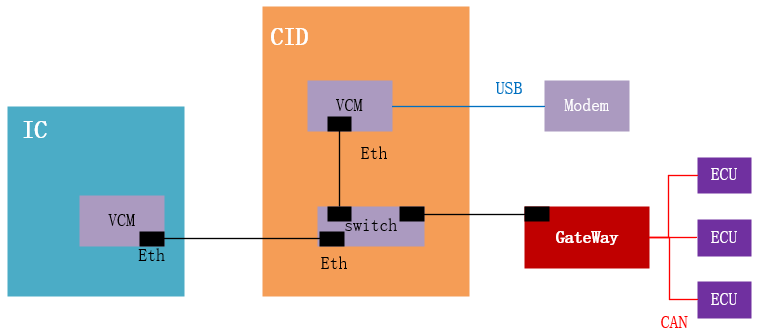
通过网关芯片上的文字和标致信息,研究员很容易就确认了网关芯片的型号:“Here we show the gateway with CAN transceivers. Similar devices are often found in CAN gateways. The gateway is connected to the CAN buses and the Ethernet switch. We believe the firmware on the gateway is FreeRTOS, a light-weight real-time operating system (RTOS) with multiple automotive uses.”2.11 “自报家门”第四弹:Modem信息确认
同样地,通过Modem芯片上的文字和标致,研究员很容易就确认了Modem的型号。
2.12 软件架构的胜利:无法被找到的eCALL
研究员尝试从CID中寻找eCALL和短信相关的应用,但是没有发现任何踪迹,因此推测相关应用功能的实现均在Modem中。由于Modem没有暴露攻击接口,因此没有进一步对Modem进行分析。“Most TCUs in vehicles do not allow user-accessible and swappable SIM. Embedded or inaccessible SIMS are becoming the norm. Despite further examination of the Tesla, we did not uncover any functionality for tracking or eCall running on the CID’s VCM. This suggests these safety and security features run directly on the cellular modem, as per TCUs in other vehicles.”从攻击者的思路反思,我们在做正向设计的时候,应该尽量避免复杂的架构,好的设计是将同一功能的模块封装在同一个芯片中,并尽量减少芯片的攻击面。在实际的设计中,eCALL等功能模块(的部分功能)经常被放到IVI中(类似于这里的CID),这种设计明显增加了eCALL及Modem被攻击的可能性。2.13 芯片封装方式的第一次胜利:BGA阻止对Modem的侵入式分析
由于Modem芯片的封装方式使用的是BGA,这种封装方式的特点是拆卸难度和重新挂载的难度都很高,因此研究员放弃了从Modem芯片中还原固件的尝试。“Recovering firmware from a Sierra Wireless AR8522 module without causing damage is extremely difficult, being as it is a tightly packed BGA module with numerous BGA chips, all contained under a soldered-on shield”2.14 芯片封装方式的第二次胜利:面朝下的WIFI和蓝牙模块
由于WIFI和蓝牙模块的芯片均采用正面朝下的封装,这种封装方式有效地隐藏了芯片的文字信息,因此攻击者无法直接获取芯片型号。再加上芯片使用BGA的封装方式(根据上下文可以推测其封装方式也为BGA),拆解难度极大,因此有效地阻止了研究员的进一步攻击。“The CID employs a Parrot Wi-Fi and Bluetooth module, mounted face-down. We could not confirm the specific model because it could not be removed from the main board.”2.15 不设防的物理接触之二:即拆即用的SD卡
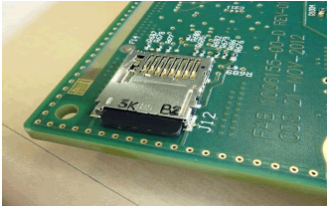
SD卡没有完整性校验机制,存储升级期间使用的firmware,并且根据文章的描述,SD卡的存储内容应当为明文存储,这意味着攻击者可以很容易地从SD卡提取数据及向SD卡中写入数据。在第二阶段的攻击过程中,攻击者很好地利用了SD卡的不设防。“On top of the CID main board are two socketed SD cards. The CID has to be taken apart to access a 4GB normal SD card. It is connected to the gateway and used for staging files during the firmware update.”2.16 通信协议的第一次胜利:验签指令阻止VCM进入Recovery模式
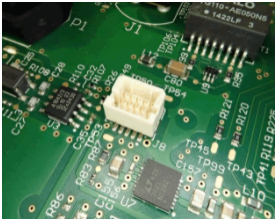
CID内部包含USB接口,该USB连接VCM,用于使VCM进入recovery模式,但指令存在签名校验,因此攻击者没能成功进入Recovery模式。“There is a single USB port on the CID main board connected to the VCM. Previous investigation (https://blog.lookout.com/hacking-a-tesla), discovered this could be used to gain access to a Tegra recovery mode (RCM). This had not changed; it cannot be disabled. This was still protected by security meaning that commands have to be signed before they are accepted.”2.17 成本战的第二次胜利:阻止对USB漏洞的利用
因为担心利用USB漏洞导致硬件损坏,研究员放弃了对USB公开漏洞的利用,硬件的高成本再次阻止了攻击者。“The Fusée Gelée vulnerability was found in the RCM bootloader in 2018. Malicious USB packets could bypass security as a result. We confirmed with the researchers who discovered this vulnerability that it is likely to be present on the earlier Tegra SoCs used by VCMs in the Tesla. We decided not to try and exploit this vulnerability due to the risk of rendering the VCM inoperable.”2.18 通信协议的第二次胜利:握手协议和VPN阻止对车云通信的攻击
CID与server通过以太网口通信,网络走VPN连接,且存在安全握手协议,没有可直接利用的点。“On the CID, two Ethernet ports are exposed, using proprietary automotive connectors. Previously fully open, one is a dedicated diagnostic connector. This is now secured via a proprietary handshake and has no known vulnerabilities. A “seed” is sent from Tesla servers to and from the CID via VPN connection.”2.19 通信协议的第二次破防:不设防的诊断接口
OBD口没有隔离和访问控制,可以发送任意CAN命令。“No sign of segregation or access control was observed – if someone had access to this port they could sniff and send arbitrary CAN traffic.”2.20 芯片封装方式的第三次胜利:BGA阻止对多个芯片的JTAG分析
BGA封装方式阻止了研究员对多个芯片JTAG管脚的分析尝试。“The only package with accessible pins and JTAG is the Analog Device ADSP-21489 – the rest are BGA.”2.21 成本战的第三次胜利:硬件成本击退了对JTAG接口的分析
研究员通过PCB上的布局大致推测了JTAG接口焊接的位置:“It looks like they may be JTAG connections because these are all near microcontrollers or memory devices”并且提出了两种可行的破解思路,但由于存在损坏硬件的风险,研究员放弃了进一步的破解尝试。
“Several methods are available to determine the pin-out:1、Brute-force JTAG testing (“JTAGulating”) – can produce false positives and damage the board 2、Continuity tests to known JTAG pins on one of the devices are reliable if pins can be accessed and datasheets are available“
2.2 安全木桶的短板:唯一一个非BGA封装的芯片
音频处理器的封装方式没有采用BGA,暴露了芯片管脚。“The only package with accessible pins and JTAG is the Analog Device ADSP-21489 – the rest are BGA.”我相信特斯拉的安全工程师曾经对音频处理器的封装方式提过要求,因为仅有一个芯片没采取BGA的封装方式。这个零部件的供应商可能只想沿用旧的方案,而不想对现有硬件做任何修改,包括仅仅修改芯片的封装方式,因为改动即意味着额外的成本。这种问题在整车领域是一个很普遍的问题,很多供应商都以平台化的方式提供零部件,并拒绝做出任何定制化的服务,其中国外的供应商在这方面表现尤其突出。往更大的方面说,这也是传统车企转型慢的一个重要原因,因为一个车型的供应链及其庞大和复杂,即使车企求变,供应链也不会立刻就响应你的变化。另外,传统车型的研发团队,对旧有方案驾轻就熟,沿用旧的方案是他们的不二选择。供应链和车厂本身存在的守旧派,是传统车型求变的一大阻力。2.23 “自报家门”第五弹:音频处理器信息确认
根据音频处理器上的文字和标致,研究员确认该处理器的型号是ADSP-21489。“The only package with accessible pins and JTAG is the Analog Device ADSP-21489 – the rest are BGA. ”2.24 被“近亲”研究再次突突了一小步:研究员获取音频处理器datasheet
通过ADSP-21489音频处理器的型号,研究员获取到了该芯片的datasheet,根据datasheet中芯片管脚的定义,研究员找到JTAG相关的管脚并进行了连接和测试,但是没有发现安全漏洞。“The only package with accessible pins and JTAG is the Analog Device ADSP-21489 – the rest are BGA. The JTAG connector pin-out could be determined because the datasheet and pinout were available. We used social media to identify and order the specific type of connector. We made a cable and used a variety of JTAG adapters and a logic analyser to ascertain if any security had been enabled.”虽然连接JTAG后没有发现安全漏洞,但这里暴露了一个很严重的问题,就是来自供应商的平台化方案隐含的风险。我相信ADSP-21489是一个应用广泛的音频处理器,因为能从网络上能够轻易获取datasheet的芯片,不太可能是冷门的产品,用的人多了datasheet才可能广为流传。从业务成本收益的角度来看,平台化的方案能够有效地降低成本,并且装机量越高边际成本越低。但是从安全的角度来看,这种广泛使用的平台化方案,更加容易暴露风险,并且将整车的安全风险管理周期从车型的生命周期提前到了零部件的生命周期,即当我们的车型还没有开始设计的时候,相关的风险就已经暴露了,因为即将使用的零部件的datasheet被泄露了。2.25 通信协议的第三次胜利:安全调试阻止对JTAG的调试访问
虽然成功连上了音频处理器的JTAG,但是研究员却没能成功执行任何调试命令,因为解锁JTAG需要一个64位的口令。研究员甚至尝试了可能的默认口令,但还是失败了。“We tried JTAG commands but the VCM on the CID and IC did not respond, leading us to think that it is likely that access is prevented due to blown SoC fuses. Using the “censorship” functionality provided by the MPC56xx series, a JTAG ID elicited a response from the gateway processor. This uses 64bit password protection. We tried the default value of FEEDFACECAFEBEEF without success. We ruled out brute-forcing this; firmware could be obtained using other methods. ”2.26. 成本战的第四次胜利:昂贵的JTAG适配器让攻击者放弃进一步攻击
针对JTAG,还有一种可能有效的手段是使用特殊的JTAG适配器,但是因为这种适配器的价格比较昂贵,需要花费1200英镑,并且研究员推测即使使用了这个适配器,最终的效果也不会太好,因此放弃了购买适配器做进一步的攻击。“JTAG ID elicited a response from the ADSP-21489, but it seemed to be using 64bit password protection. This proprietary protection scheme requires a specific JTAG adapter. This would cost about £1,200 and probably merely confirm that access is not possible. We believe it would be unlikely to pose any immediate security risks. ”
3.1 成功击退攻击者的安全措施
纵观此次针对特斯拉的硬件攻击,我发现如下几种防护措施起到了很好的保护效果:
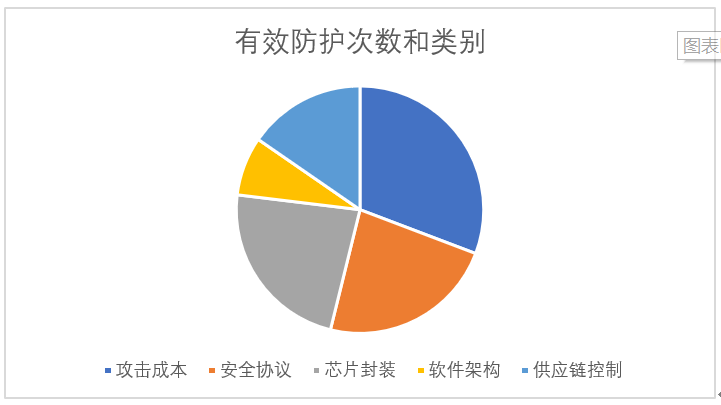
3.2 各类防护形式的效果
对每次形成有效防护的技术做归类和统计,我发现攻击者出于攻击成本的考虑放弃进一步攻击的次数最多。但需要注意的是,我的统计样本有限,可以作为本文的结论,但不具备普遍性。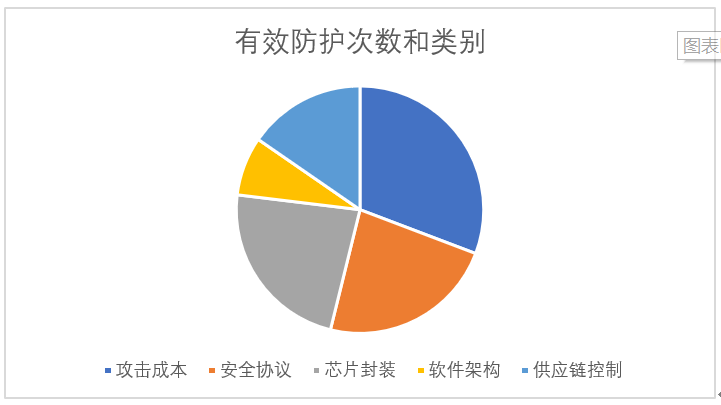
此攻击案例暴露的弱点类型较多,其中我认为最严重的是芯片信息的泄露,使得逆向重组硬件架构和通信架构毫无阻力。1) 固件明文存储在Flash中,应该采用加密存储,例如很多芯片提供OTF的功能,如果有该功能应该尽量使能
2) TCM生命周期的管控不严,旧的零部件流转到市场。应该制定完整的零部件生命周期管理策略,在售后、维修和报废环节及时回收旧的零部件,防止外流。3) 插槽式的SD卡可被任意安装和卸载,SD卡存储内容未做保护和加密。
有些风险从芯片的生命周期就开始了,车型还没诞生,但相关的风险已经开始暴露了,具体包括:1)旧方案的延续性,硬件的沿用,软件的复用等等,都可能造成安全方案不能及时迭代和更新。2)供应商安全能力的先天不足。这种情况下,即使OEM有安全要求,但供应商确实没有安全能力来实现安全能力,也会导致产品中出现安全短板。
参考文章
https://www.pentestpartners.com/security-blog/reverse-engineering-tesla-hardware/
看雪ID:kxliping
https://bbs.pediy.com/user-home-890008.htm
*本文由看雪论坛 kxliping 原创,转载请注明来自看雪社区
在线申请SSL证书行业最低 =>立即申请
[广告]赞助链接:
关注数据与安全,洞悉企业级服务市场:https://www.ijiandao.com/
让资讯触达的更精准有趣:https://www.0xu.cn/













 关注KnowSafe微信公众号
关注KnowSafe微信公众号